Whoa! This has been a long time coming. I used to fumble through private keys on paper slips and sticky notes, which felt prehistoric even back then. My instinct said there had to be a cleaner way to manage NFTs on Solana without sacrificing security or sanity. After testing extensions, mobile bridges, and a handful of sketchy sites, I landed on workflows that actually make sense for everyday collectors and creators.
Really? Wallet extensions can be that usable. Most people picture clunky pop-ups and tiny address strings that you have to copy-paste like you’re defusing a bomb. The reality is softer now—UX improvements have made on-chain actions feel like pushing buttons in an app, though obviously there’s still risk. I’m biased toward tools that minimize friction, because the less you fumble, the fewer mistakes you make, right?
Here’s the thing. NFTs on Solana are lightweight compared to Ethereum, which matters for speed and fees. That speed lets you dart between marketplaces and mint pages without waiting forever or paying a small fortune. It also means browser extensions can give near-instant feedback during transactions, so you see confirmations fast and move on. That immediacy changed how I approached drops and secondary trades.
Wow! The first time I watched a mint go through in under a second I nearly spilled my coffee. Seriously, that rush of watching a transaction finality hit so quickly is addictive. But fast is not always safe—I’ve seen social engineering pushy enough to get people to approve weird requests. My gut feeling during those moments was: pause, read, and if somethin’ smells off, disconnect the site.
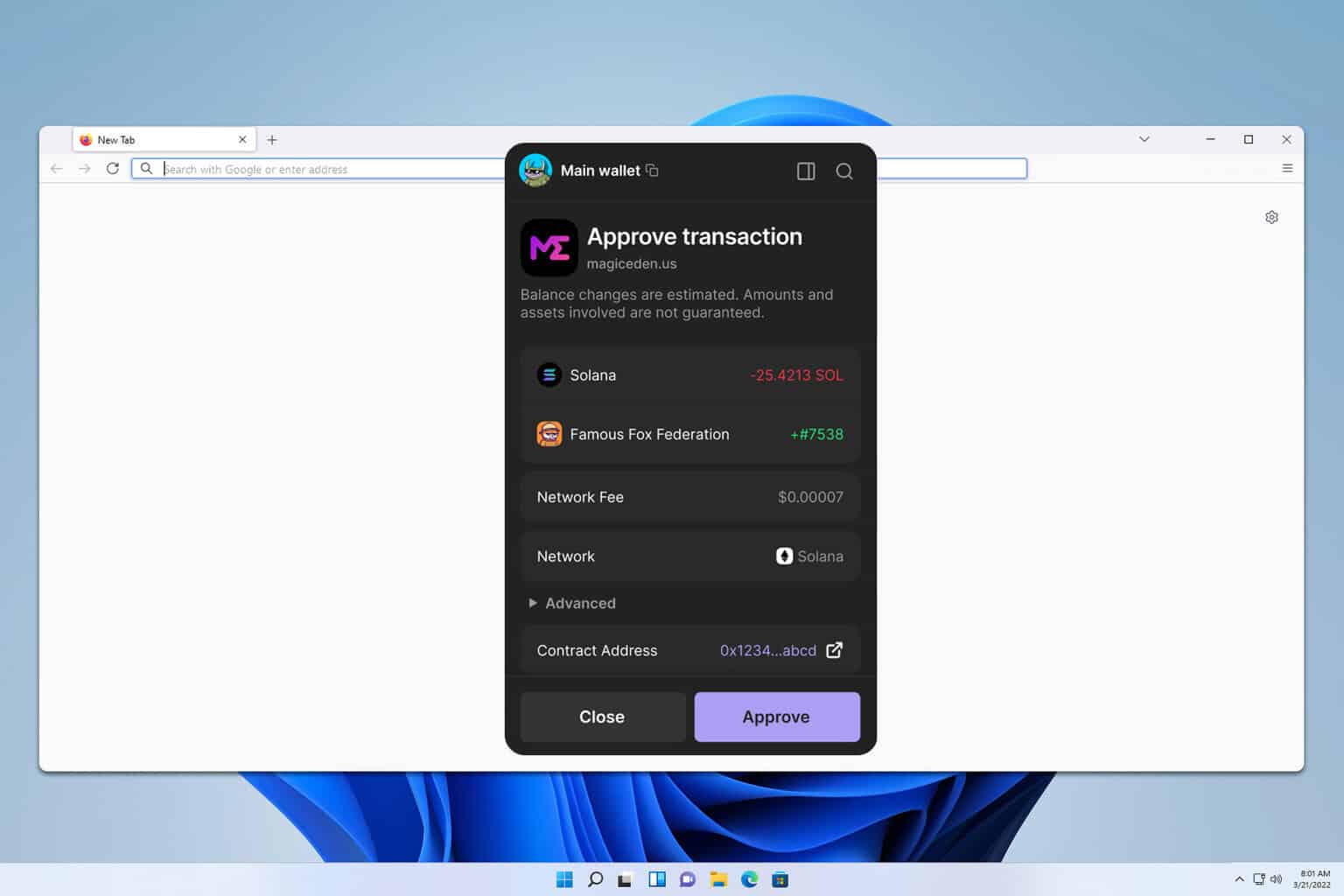
Here’s a quick checklist I now run before clicking approve. Check the site domain and wallet request details. Confirm the token and network match what you expect. Consider whether the permission being asked for is permanent or one-time. If any of those items are fuzzy, cancel and re-evaluate in a minute or later, because approvals can be revoked only with extra friction.
Whoa! Installing a browser extension is trivial, but security practices are not. When you add an extension, the browser grants it power—sometimes more than you’d like. I always set up a new wallet with a hardware-backed seed phrase when possible, and then use the extension as a daily driver with limited spend limits. On one hand convenience matters, though actually, wait—let me rephrase that: convenience matters, but not at the cost of a single point of failure.
Really? I used to think multiple hot wallets were overkill. Now I run a separate account for minting and a different one for holding blue-chip pieces, which keeps exposure limited. Initially I thought a single vault was simpler, but then I realized the blast radius from a compromised session is much bigger than the hassle of hopping between accounts. This is the kind of trade-off that feels annoying until it saves you thousands (or more).
Here’s the part that bugs me about many guides: they gloss over permissions. Extensions will ask for things like «connect,» «sign transaction,» or rarer rights like «sign arbitrary data.» Those last ones are red flags in many scenarios. My working rule: never sign arbitrary data unless you know exactly what that data does, because it’s essentially granting a script the ability to act with authority in your name.
Wow! UI details actually help you avoid mistakes. Good extensions show clear request modals with origin info and exact token operations spelled out. Bad ones hide details behind terse labels that say «Approve» with no context. If a modal doesn’t explicitly show the token mint, destination address, or SOL amount, that’s a big nope from me.
Here’s a moment where experience shaped my expectations. At first I trusted any wallet with a slick design. Then a phishing clone almost snagged me because it looked identical at a glance. On one hand visual polish inspires trust, though on the other hand polished fakes exist—so the lesson was to validate origins, double-check extension IDs, and pin trusted extensions in the browser. I keep a shortlist of verified extension IDs somewhere offline; it sounds extreme, but it’s saved me from clicking the wrong thing once or twice.
Really? Let me tell you about the phantom wallet experience. Installing it took about two minutes, and the onboarding flow walks you through seed setup and a password for quick unlocks. The approval modals are readable, and the token list syncs cleanly with Solana networks, which matters if you hop between mainnet and testnet. I found the extension strikes a reasonable balance between approachable UX and explicit security prompts.
Whoa! There are still edge cases that make me nervous. For example, wallets sometimes cache approvals longer than I’d like, or marketplaces request re-approvals on seemingly unrelated actions. This inconsistency can be confusing when you’re in a hurry. My analytical side dug into the transaction logs a few times to confirm what’s changing under the hood, and that habit helps decode strange prompts.
Here’s a practical flow I use for mint drops. Prepare funds in the extension ahead of time, open the mint page in a fresh window, and connect only when the queue starts moving. If a bot or mint script asks for delegation or fancy permissions, stop and read it fully. If the mint fails, check recent failed transactions to see whether you accidentally approved a different token or a phishing contract—sometimes the nuance is subtle and easy to miss in the heat of the drop.
Really? Token metadata can be a sneaky source of error. A mispointed metadata URI or a renamed collection can disguise an imposter piece. I rely on community verification—trusted collection handles on Discord or verified badges on marketplaces—and I cross-check mints against on-chain records. Initially I wanted to trust marketplaces to police everything, but collectors and creators often spot scams faster than platforms do.
Wow! Syncing across devices matters more than I expected. Extensions plus mobile wallet adapters let you bridge approvals from a phone when you’re away from your desktop, which is handy at events or shows. However, mobile bridging introduces another attack surface, so I use it selectively and only with reputable apps. (oh, and by the way… I still prefer to avoid approving large spends from a coffee shop Wi‑Fi.)
Here’s a deeper trade-off I wrestle with: convenience versus custody. Custodial platforms remove a lot of the UX friction, but they also centralize control and become targets for hacks. Non-custodial extensions keep control in your hands, though they require discipline. For many creators and collectors, a hybrid approach—keeping the bulk in cold storage and using an extension for daily activity—feels like a very practical compromise.
Really? Backup rituals are boring but essential. I wrote down my seed in triplicate and stored copies in different locations. That felt very old-school—like burying a time capsule—yet it gave me calm during an accidental OS reformat. If you’re not comfortable with that, consider a hardware wallet that integrates with your extension, because hardware wallets make the signing step explicit and physically present.
Wow! Community stuff matters. Local meetups in NYC and San Francisco taught me to ask questions out loud and to bring screenshots if something looked weird. The community will usually point out red flags you missed, and there’s a level of social accountability that prevents dumb mistakes. Also, sharing workflows taught me hacks I’d never thought of, like batching approvals when moving many NFTs between accounts to save time and fees.
Practical tips and final habits
Okay, so check this out—my daily checklist is simple and repeatable. Unlock the extension, verify network, confirm balances, read the approval modal fully, and sign—only if everything matches expectations. Small rituals like these reduce cognitive load and prevent those «oh no» moments when you spot a wrong address later. I’m not perfect; I’ve made dumb mistakes, but a routine catches most of them and gives you a consistent baseline to iterate from.
Here’s what I avoid: signing transactions that include «delegate» without understanding long-term implications, using public computers for approvals, and approving unfamiliar sites even if they’re heavily hyped. I’m cautious about browser permissions, I limit extension count to reduce attack surface, and I update the extension as soon as a security patch drops. It may sound strict, but once these habits stick, they become second nature.
FAQ
Do I need a separate wallet for NFTs and SOL?
Short answer: it’s a good idea. Using separate accounts limits exposure and keeps day-to-day activity isolated from long-term holdings. Your mileage may vary, but for collectors who value safety without too much friction, splitting responsibilities between wallets is a practical balance.





Deja una respuesta